
If you want to run Windows 10 on a Mac there are really only two options worth considering: a native install using Boot Camp or virtualization through Parallels. Each is excellent in its own right, but which one best meets your needs?
Trying to answer that question can prove to be a daunting task for many Mac users, based on my experience. The conundrum: Boot Camp is easy to use and readily available in OS X, while Parallels is the most versatile software of its kind for OS X. It's not easy. Fortunately, this article will help you understand which one is right for you.
Fundamental Differences
To start, let's talk about what sets Boot Camp and Parallels apart.
Apple has created Boot Camp with the goal of making it easy for Mac users to natively install Windows on their device, alongside OS X. The tool, which officially supports Windows 10, will create a bootable USB installation media of the operating system, adding the necessary drivers for your Mac in the process.
It also helps you partition the drive, and, after everything's done, it will even restart your Mac so that you are taken right to the initial Windows 10 setup process. As long as you have a large-enough USB drive and a Windows 10 ISO file, Boot Camp will help you get the job done with as little effort as possible.
And since traditional PCs and more-recent Macs are very similar hardware-wise, Windows 10 will run on a Mac pretty much like it would on a, say, Dell or HP laptop or custom-made desktop. You may notice some kinks here and there, depending on how polished the drivers are and whether Windows 10 supports all the features that the Mac offers, but, for the most part, it will all work as expected.
Now, on to Parallels. But, before we dive into it, a quick note: the virtualization software has added support for Windows 10 in its 11th iteration, which is the latest available at the time of writing this article. So, for all intents and purposes, you can look at this article as a comparison between Boot Camp, in its OS X 10.11 El Capitan form, and Parallels 11.
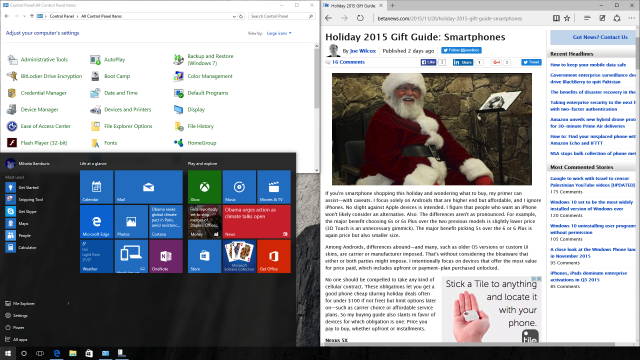
But why Parallels? I have mentioned that it is extremely versatile, and that is because Parallels has a dual personality. It can let you run Windows 10 in a typical virtual machine, but it can also allow you to run only the Windows program that you want. Chose it from the list of available software, and it will shortly appear on the screen like an OS X app.
The latter, called Coherence mode, is what makes Parallels special. When this mode is enabled, you get the best of both worlds: the ability to experience OS X in all its glory while getting to keep all your favorite Windows programs close. And it works great.
Why You Should Choose Boot Camp
Now that you know Boot Camp and Parallels' features, let's talk about benefits. I'll start with Boot Camp, because it is what every OS X user has easy access to.
Boot Camp is best at one thing, and that is allowing you to run Windows 10 at full speed on a Mac. It will give you the best performance, and a PC-like experience, with all the benefits and drawbacks that come with it.
Since you are not using virtualization, your Mac will perform under Windows 10 just like a similar desktop or laptop. Boot Camp presents an understandable advantage when used on an entry-level Mac with a slower processor and not a lot of RAM, because the device will only have to run a single operating system and not two at once.
In my experience with Windows 10 installed via Boot Camp on my late-2013 MacBook Air I have had no noteworthy issues to speak of. Like I mentioned earlier, there are some niggles here and there but, once everything is set up as you want, you'd be hard-pressed to tell the difference between your Mac and a traditional PC.
If you want to switch back to OS X, you can easily do so by opening Boot Camp in Windows 10 and selecting the option to boot to OS X. Or you can press the Option/Alt key on your Mac keyboard right after the device powers on or reboots.
It should be noted that the Apple drivers and software do not reveal anywhere near the same level of customization as they do in OS X. To give you an idea of what I mean, you get lots more touchpad gestures under OS X than Windows 10. Also, battery life seems to be affected by the transition to Windows 10, as Microsoft's operating system and/or Apple's drivers are not well optimized for this scenario.
Why You Should Choose Parallels
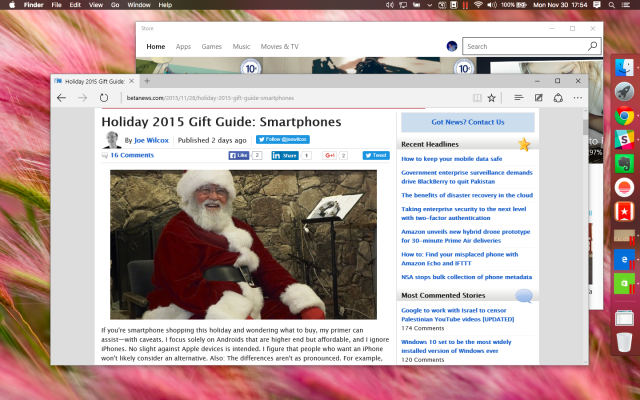
Parallels lends itself to both users who need to have Windows 10 running alongside OS X, but also to those who just want access to Windows programs alongside OS X apps. The beauty of it is that switching between these two modes is done by simply entering or exiting Coherence mode, which is an option easily accessible from the virtual machine's menu bar.
Those who want to run Windows 10 in a typical virtual machine will find that the operating system runs very well with no issues to speak of. Meanwhile, those who just want to run, say, Microsoft Edge or Cortana will only get that program and none of the Windows strings that typically have to come with it. You can't really fault Parallels for doing anything wrong. It just works, no matter what you're trying to achieve.
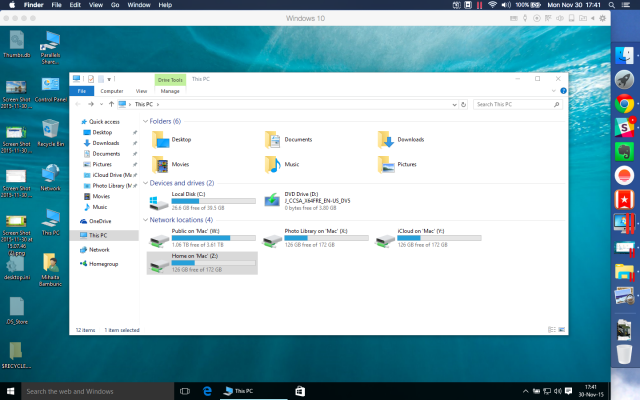
Parallels also makes it extremely easy to access Windows files on OS X and vice-versa. When using Windows 10, your Mac's Home, iCloud, Photo Library are mounted as network drives, which makes it extremely easy to share content between the two devices (the Mac and the virtual machine). When you're in OS X, just open Finder and you will see your Boot Camp installation listed under Devices; open it and you will see the contents of your C drive under Windows 10.
Parallels is also very flexible, as it can be configured in all sorts of ways depending on what you are trying to do. You can give priority to the virtual machine, for the best-possible performance of Windows 10 under virtualization, or the Mac, so that it runs well while powering that Windows 10 VM.
You can choose how much RAM you want to allocate, how much storage space you want to allocate, give spoken commands, add some password protection, choose what sort of access other devices have to the VM, set up shortcuts and much, much more. If you are a power user, you will love it.
Now, where Parallels and virtualization software in general does not shine is overall system performance. What I mean by this is that Windows 10 in a virtual machine will not be as fast as Windows 10 running natively on the Mac. That is an obvious downside, but it is worth pointing out based on some conversations I have had with some folks in the past.
Also, Parallels is not free. For home users and students, Parallels 11 costs $79.99 per year from Parallels' site. A subscription-based version, called Pro edition, is priced at $99.99 per year, also on Parallels' site. All this convenience and versatility comes at a cost. But, I think, it is absolutely worth it.
So?
My recommendation is to get Parallels. In most cases it is the better option. Not to mention that it makes more sense to add new capabilities -- namely, to run Windows 10 in a VM and/or Windows programs straight from the OS X dock -- to your Mac than limit yourself to just a single operating system or collection of programs at a time -- why should you?
But, to play Devil's advocate, Boot Camp shouldn't be ignored if you will rarely be using Windows 10 or needing Windows programs. For instance, if you want to play a game from time to time, Boot Camp makes more sense because it gives you better performance.
So, what will you choose?
Photo credit: rvlsoft / Shutterstock
